In today’s digital age, securing WiFi from hackers is more judgmental than ever. With the growth of internet-connected machines, the danger of cyberattacks has grown significantly. Hackers can readily enter your WiFi web if you do not take proper safety measures, leading to data theft, unauthorized entry, and even individuality fraud. This article will discuss protecting your WiFi network from hazards and securing your digital life’s safety.
What is WiFi Security?
Securing WiFi from hackers is crucial for protecting your wireless network from unauthorized access and cyber threats. Adequate WiFi security involves several key steps, including setting solid passwords, enhancing encryption protocols, and employing network monitoring tools. Following these practices can significantly reduce the risk of hacking attempts and ensure a safer online experience.
Why Hackers Target WiFi Networks
Hackers often target WiFi networks to swipe personal data, such as passwords, economic details, and diplomatic documents. They may also use your network to perform criminal actions, which can lead to harsh results for the network owner.
Setting Up a Strong Password: Importance of a Strong Password
A strong password is your first line of protection against hackers. It stops unofficial users from recovering your network and ensures that only licensed devices can connect.
-
Tips for Creating a Strong WiFi Password
- Use uppercase and lowercase notes, digits, and memorable personalities.
- Bypass familiar words, words, or fast guessable data like birthdays.
- Make a password that is at most minuscule 12 symbols long.
- Modify your password regularly to keep it safe.
-
Changing the Default Router Password
Multiple routers have default passwords that are comfortable to remember. When you set up your router, change the insolvency password to a strong, unique one. It will stop pirates from accessing your router’s settings and creating unauthorized changes.
Encrypting Your WiFi Network: What is WiFi Encryption?
WiFi encryption is the process of encoding data transferred over your wireless network to control uncertified access. Only machines with the correct encryption key can read the data.
-
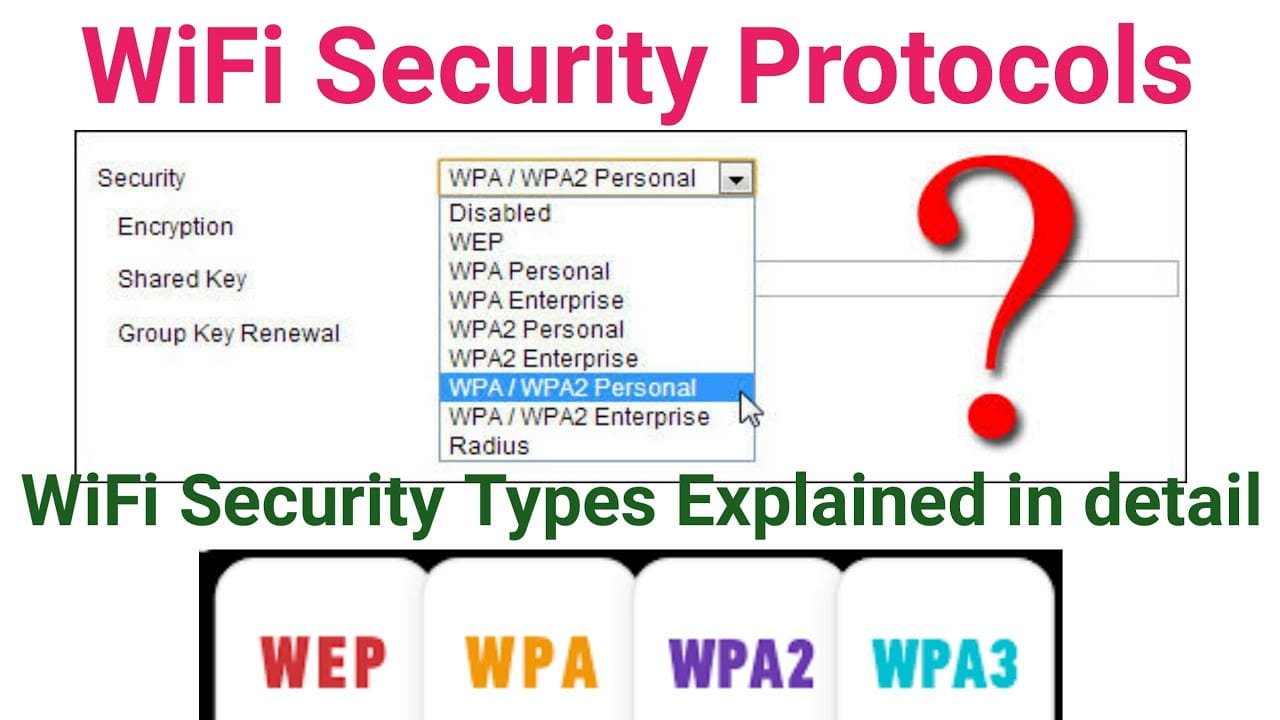
Types of WiFi Encryption
- WEP (Wired Equivalent Privacy): An older, small, safe encryption process.
- WPA (WiFi Protected Access): An enhanced but ancient encryption method.
- WPA2 (WiFi Protected Access II): A positively safe encryption method widely used today.
- WPA3 (WiFi Protected Access III): The most outstanding and secure encryption standard.
-
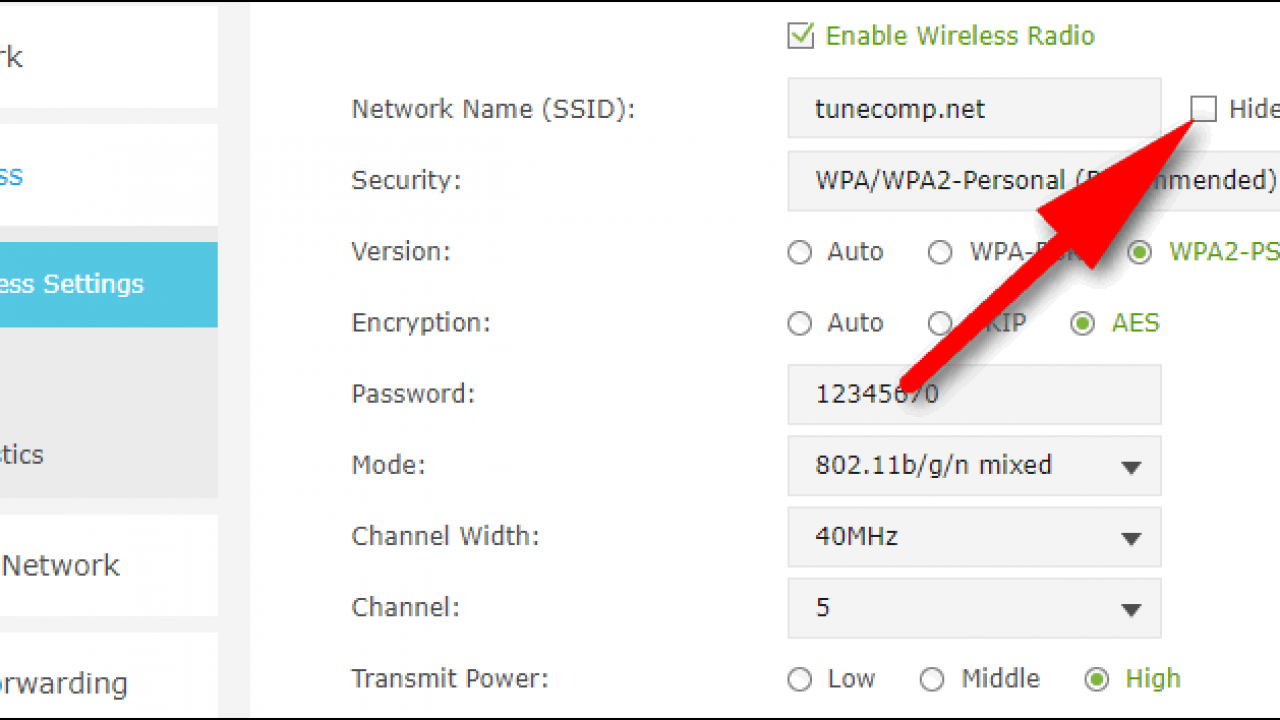
How to Enable Encryption on Your Router
You can access your router’s surroundings via a web browser. Navigate to the security or wireless settings section. Select WPA3 (if available) or WPA2 as your encryption method and set a robust and unique password.
Why Firmware Updates Are Important
Router software updates often include security patches that resolve exposures. Frequent updates confirm that your router is secure against the latest threats.
-
How to Correct Your Router’s Firmware
Check your router factory’s website for the most delinquent firmware performance. Download the update and follow the education to install it. Many current routers also offer automated firmware updates.
-
Setting Up Automatic Firmware Updates
Enable automated firmware updates in your router’s settings to ensure you still have the latest safety patches without not mechanically preventing them.
What is MAC Address Filtering?
MAC (Media Access Control) talk filtering lets you choose which devices can link to your web based on their unique MAC lessons.
-
How to Implement MAC Address Filtering
Access your router’s settings and add the MAC addresses of your trusted devices. This limits network access to only those devices.
-
Benefits of a Guest Network
A guest web lets visitors connect to the internet without retrieving your primary network. This detachment contains potential safety risks from visitors’ devices.
-
How to Set Up a Guest Network
Access your router’s settings and enable the guest network feature. Set a separate, strong password for the guest network and configure its settings to restrict access to your leading network.
-
Managing Guest Network Settings
Regularly update the guest network password and watch related devices to ensure only authorized users’ keys.
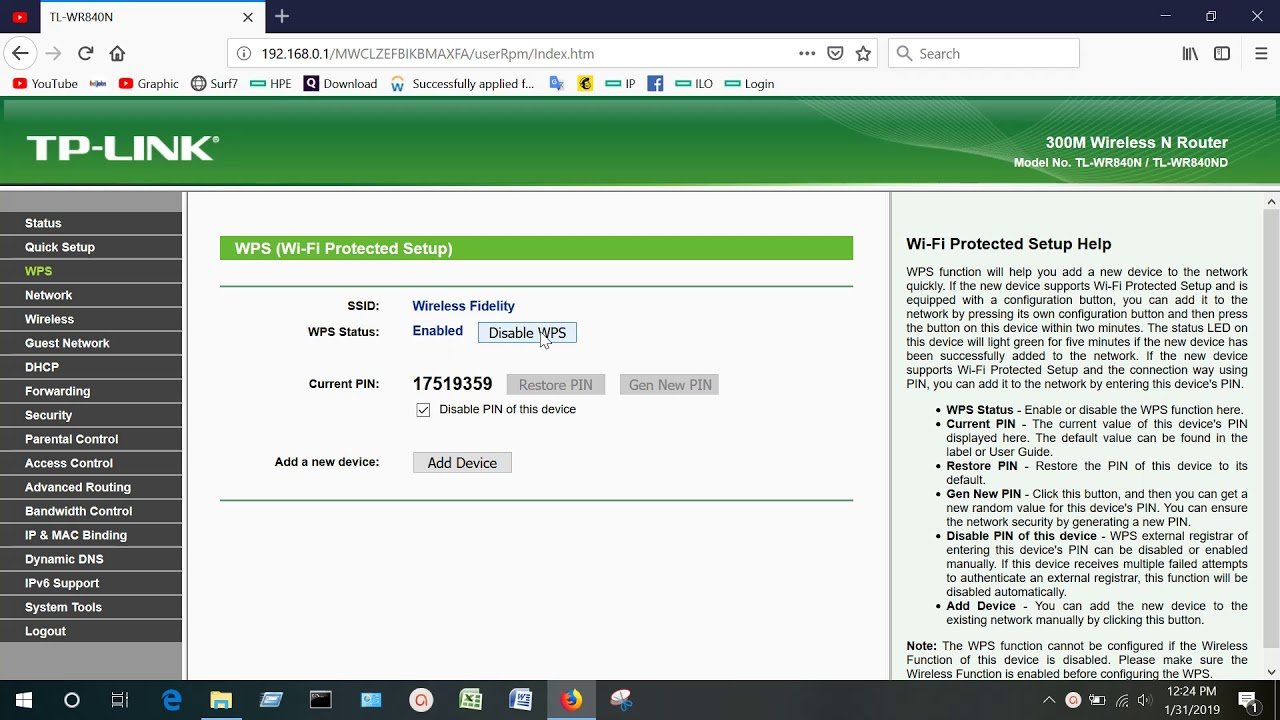
Disabling WPS (WiFi Protected Setup): What is WPS?
WPS is a component that permits machines to link to a WiFi network efficiently by utilizing a PIN or making a router control. While suitable, it can also be a safety risk.
-
Why Disabling WPS Enhances Security
WPS PINs are weak to brute force attacks, making it more comfortable for pirates to access your web. Maiming WPS eradicates this chance.
-
Steps to Disable WPS on Your Router
Use the guide to your router’s settings to find the WPS setup. Turn off the feature to enhance your network’s security.
Hiding Your SSID: What is an SSID?
The SSID (Service Set Identifier) is the name of your WiFi grid. Bankruptcy is an issue so nearby machines can see and relate to it.
-
Pros and Cons of Hiding Your SSID
Pros:
It makes your network less visible to casual users.
Cons:
- Advanced hackers can still find hidden networks.
- It can make it harder for your own devices to connect.
-
How to Hide Your SSID
Access your router’s settings and turn off the SSID broadcast feature. You can typically find it in the wireless or security settings section.
Enabling Network Firewalls: Role of a Firewall in WiFi Security
A firewall monitors and handles incoming and outgoing web traffic based on secured protection rules. It serves as a border between your network and possible risks.
-
How to Enable the Router’s Firewall
Most modems come with a built-in firewall. To enable it, enter your router’s settings and ensure the firewall is allowed. Then, configure the settings to suit your security needs.
-
Using Additional Firewall Software
Consider using additional firewall software on your devices for an extra layer of protection. Many antivirus programs include firewall features.
Monitoring Network Activity: Importance of Monitoring Your Network
Regularly scanning your network can help you detect unauthorized access and questionable moves and take immediate action to secure it.
-
Tools to Monitor WiFi Activity
Router Logs: Check your router’s logs for a list of related instruments and actions.
Network Monitoring Software: Use tools like Wireshark or Fing to watch gridlock and remember possible dangers.
-
Identifying Suspicious Devices
Review your network’s list of connected devices regularly. If you see unfamiliar devices, change your WiFi password and update your security settings.
What is a VPN? (Virtual Private Network)
VPN (Virtual Private Network) encodes your internet link, improving security by preventing pirates from securing your data.
-
Advantages of Operating a VPN with Your WiFi
- “Improves privacy and security.
- “Defends your data from eavesdropping.
- Defend your data from eavesdropping.
-
Setting Up a VPN on Your packet
Check if your router supports VPN configurations. If so, follow the teachings from your VPN provider to set it up on your router, ensuring that all related devices benefit from the counted protection.
Why Limit Device Access?
Determining the digit of machines that can link to your network reduces the risk of unauthorized entry and helps control bandwidth.
-
How to Set Up MAC Address Filtering
MAC speech filtering lets you select which machines can link to your network. To do so, access your router’s settings, find the MAC filtering option, and add the MAC lessons of your appliances.
-
Managing Connected Devices
Review and update the list of allowed devices regularly. Remove any devices that you no longer use or recognize.
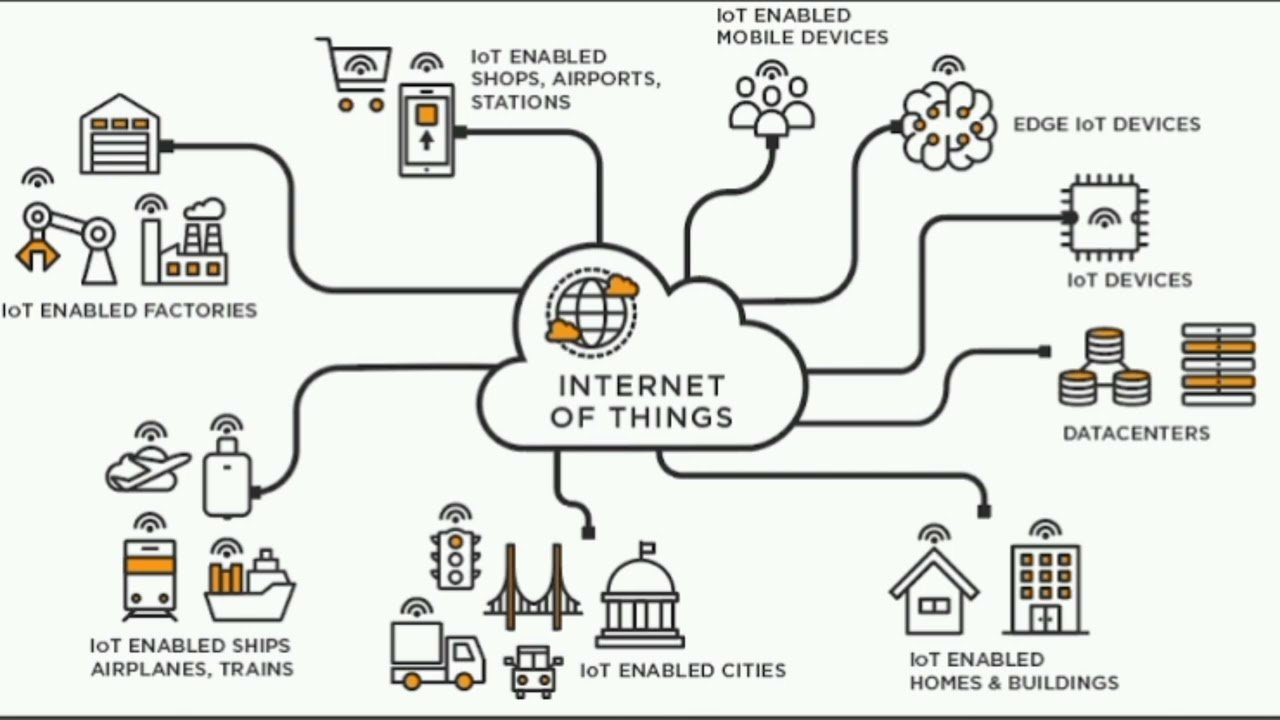
Securing IoT Devices
-
Risks Posed by IoT Devices
Securing WiFi from hackers is especially important when considering IoT (Internet of Things) machines, such as smart home devices, which often have weaker security features. These vulnerabilities make them potential entry points for hackers. Ensuring robust protection for your WiFi network is crucial to safeguard these devices and maintain the integrity of your entire digital ecosystem.
-
Tips for Securing Smart Home Gadgets
- Change default passwords to strong, unique ones.
- Keep firmware up to date.
- Disable unwarranted features that may constitute safety risks.
-
Regularly Modernizing IoT Device Firmware
Check for firmware updates regularly and use them to provide your devices with the latest security reinforcement.
Conclusion
Securing your WiFi network from hackers needs an aggressive system and regular care. Following the steps summarized in this article can significantly decrease the chance of unauthorized entry and save your private data. Stay alert and maintain your network security to deliver a safe online experience.
FAQs
How do I lock my WiFi?
How frequently should I modify my WiFi password?
Can I use antivirus software to save my WiFi network?
Is it safe to use public WiFi networks?
How do I learn if my router requires a firmware update?